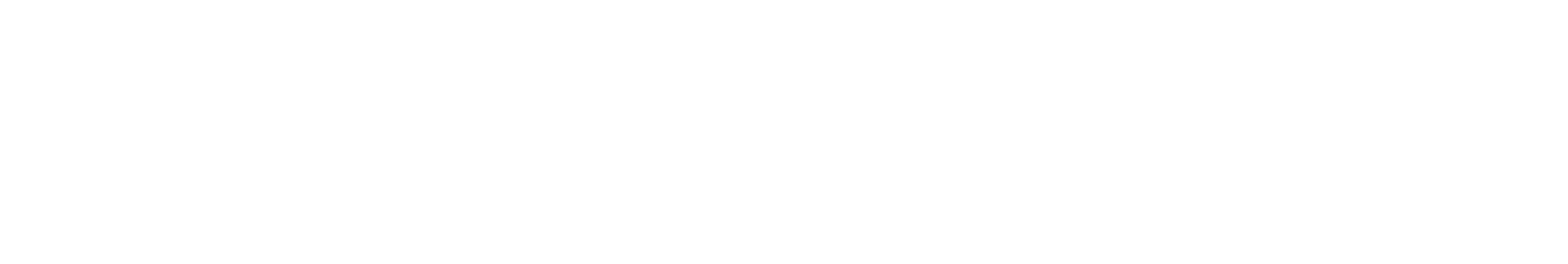
The same researcher who used Claude to find the FreeBSD kernel RCE last week just published two more zero-days. Both are in tools installed by default on almost every system you are likely to be running right now.
Vim has a remote code execution bug. The trigger is opening a malicious file. No interaction required. Just open the wrong document and code runs as your user. The patch exists. Update Vim now.
Emacs has a similar bug. It is not patched. The maintainers say it is Git’s problem.
These findings came from simple prompts to Claude. Not sophisticated red-teaming setups. Not months of research. The pattern the security community is watching emerge is becoming harder to dismiss.
The Vim Bug
Vim handles a feature called modelines. These are lines embedded in text files that tell Vim how to format the document when it opens. The feature has been around for decades. It is also the attack surface.
The vulnerability allows arbitrary command execution when Vim opens a file containing a crafted modeline. The malicious text does not need to look suspicious. It just needs to trigger the right parsing behavior. Open the file, and the command runs.
This affects every version of Vim up to 9.2.0271. The fix shipped in version 9.2.0272. If you use Vim on Linux, macOS, or any system with developer tools installed, it is probably on your machine right now. Check your version. Update if you are behind.
The reach of this vulnerability is not theoretical. Vim ships with virtually every Linux server distribution. It ships with macOS. It ships with countless embedded systems. A malicious file opened in Vim on a server could execute code with the permissions of whoever opened it.
The Emacs Bug
The Emacs issue is more complicated in a way that should frustrate everyone involved.
Emacs has a version control integration feature called vc-git. When you open a file in a directory that was extracted from an archive, vc-git automatically reads the .git/config file in that directory. If that config file contains a malicious core.fsmonitor setting, Git executes the specified program.
The attack scenario is practical. Create a zip file containing a .git/config with a crafted core.fsmonitor entry. When someone extracts the archive and opens any text file in Emacs, the payload runs silently. No prompts. No warnings. Nothing visible to the user that anything is wrong.
The Emacs team has acknowledged the vulnerability. Their position is that the problem lives in Git, not Emacs. Git’s behavior of reading and executing from .git/config in arbitrary directories is the root cause. They may be technically correct. They are also shipping a product that will get users pwned while the finger-pointing continues.
There is no patch for Emacs yet. The workaround is to avoid opening files in directories you extracted from untrusted archives. That is not a satisfying mitigation for anyone who receives zip files as part of their normal workflow.
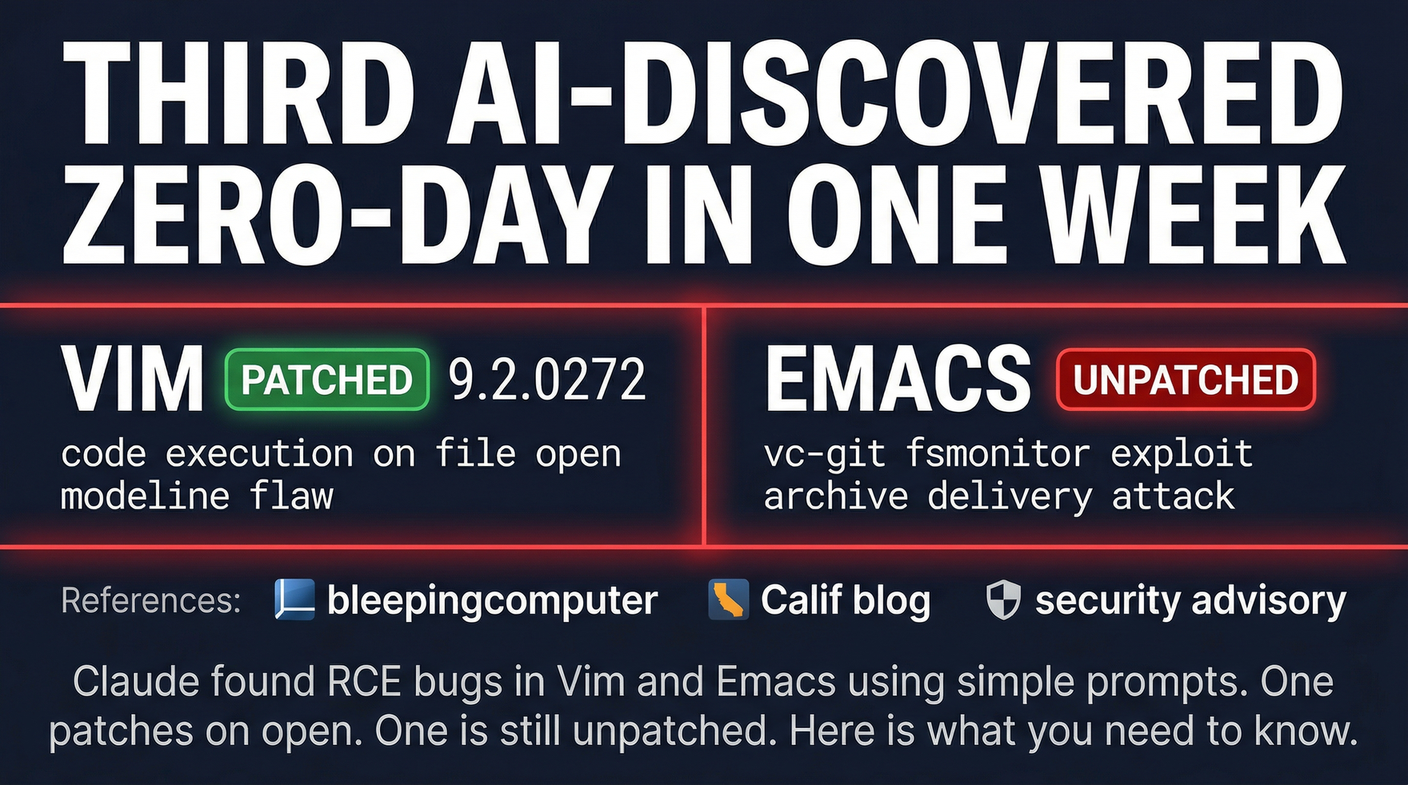
What This Week Means
Hung Nguyen at Calif published the FreeBSD kernel RCE on April 1. The Vim and Emacs findings came days later. All three were found using simple prompts to Claude. The same methodology applied to different codebases produced critical vulnerabilities in some of the most widely deployed software on the planet.
The security community is processing what this implies. Traditional vulnerability research requires expertise, time, and specialized tooling. AI red-teaming appears to lower the bar significantly. Give a capable model access to a codebase and a simple instruction to look for problems, and it finds remote code execution vulnerabilities in default-installed software.
The question is not whether this capability is real. It is whether the software ecosystem can adapt. Vulnerabilities found in hours take weeks or months to patch across the full installed base. The disclosure-to-patch timeline for AI-found vulnerabilities may be shorter than traditional research, but so is the exploitation window once the details are public.
Update Vim. Be careful with Emacs. And watch this space. The rate of AI-discovered zero-days is not slowing down.
Sources:
– BleepingComputer — Claude AI Finds Vim and Emacs RCE Bugs
– Calif Blog — MAD Bugs: Vim vs Emacs vs Claude
– Vim Security Advisory (GitHub)